Most enterprises have invested heavily in identity tools over the past decade. They have IGA platforms managing provisioning, PAM solutions protecting privileged accounts, ITDR tools detecting threats, ISPM products surfacing hygiene gaps, and multiple identity providers handling authentication. Each tool does its job. Each also creates its own data silo.
The result is that even organizations with mature IAM programs often can't answer basic questions quickly: Who has access to our most critical systems right now? Which machine identities have standing privileges they shouldn't? Where are we actually exposed across our entire environment, and what would a breach cost us?
This is the problem that Gartner formally named when it defined Identity Visibility and Intelligence Platforms (IVIP) as a distinct category in the 2025 Hype Cycle for Digital Identity. Axiad Mesh is an IVIP -- an intelligence layer that sits across your existing identity stack, connects fragmented identity data, and gives security teams a unified, continuously updated picture of identity risk across their entire environment.
For a full explanation of the IVIP category, including how it relates to ISPM, CIEM, and ITDR, see our guide to Identity Visibility and Intelligence Platforms.
What Axiad Mesh Does
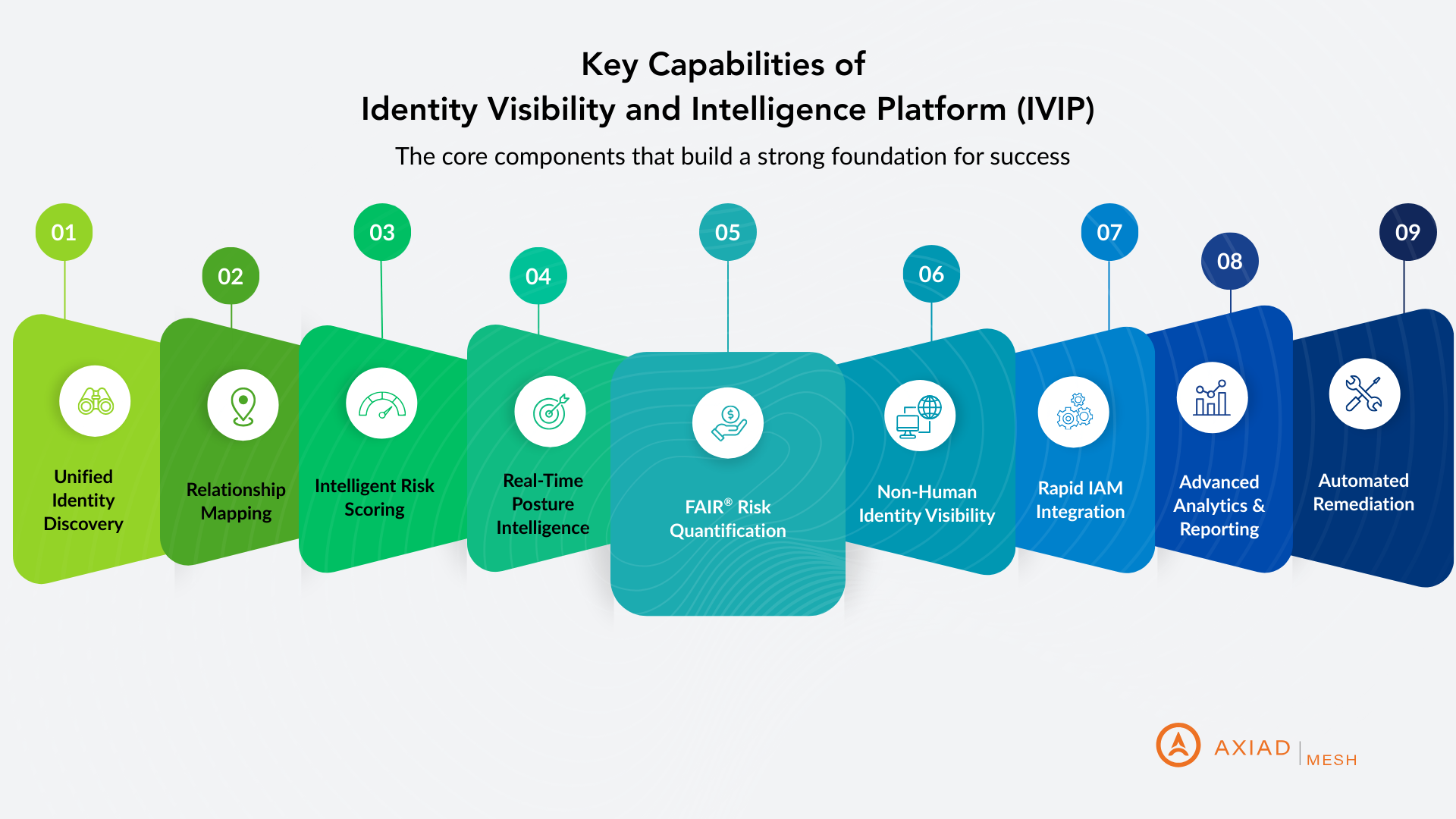
Axiad Mesh integrates with your existing IAM tools -- identity providers, IGA, PAM, ITDR, ISPM, directories, SaaS platforms, and secrets management -- and correlates identity data across all of them into a single risk view. It covers both human and non-human identities: service accounts, API keys, OAuth tokens, certificates, cloud roles, and AI agents alongside your workforce users. The platform does three things: identify risk, quantify it, and help you fix it.
Identifying identity risk across your entire environment
Axiad Mesh continuously discovers and catalogs every identity across the enterprise -- from Active Directory and Entra ID to AWS, GCP, SaaS applications, and on-premises systems. It maps the relationships between identities, permissions, and resources to surface risks that siloed tools miss: excessive privileges tied to accounts that no longer need them, weak or undeployed MFA across specific user populations, dormant accounts still active in the environment, machine identities with unchecked blast radius, and dark web compromised credentials. It also detects toxic combinations -- cases where a single identity has conflicting or compounding permissions across multiple systems that, taken together, create a material attack path.
Quantifying risk in financial terms
Axiad Mesh doesn't just flag issues -- it scores them. Every identity and identity group receives a risk score based on severity, probability, and prevalence across the environment. More distinctively, Mesh translates that risk into financial exposure using ALE (Annualized Loss Expectancy) through the FAIR methodology, giving security leaders the language to communicate identity risk to the board and justify remediation investment in business terms rather than technical ones. This is one of the capabilities that differentiates Mesh from visibility-only IVIP tools that surface findings without helping organizations prioritize or communicate them.
Remediating risk through existing controls
Visibility without action isn't security. Axiad Mesh supports automated remediation workflows, delegating fixes to your existing IAM management platforms rather than requiring manual intervention at scale. Critically, Mesh integrates directly with Axiad Conductor, Axiad's FedRAMP-authorized phishing-resistant authentication platform. When Mesh identifies authentication gaps -- weak MFA, undeployed credentials, legacy authentication protocols still in use -- Conductor provides the remediation capability to close them. This integration is what separates Axiad's approach from other IVIP platforms: Mesh doesn't just show you where your authentication posture is weak, it can actually fix it.
How Axiad Mesh Differs from Other IVIP Platforms
Several vendors compete in the IVIP category, including Veza, Elimity, Axonius, and ConductorOne. Axiad Mesh has three capabilities that distinguish it from most alternatives.
The first is native remediation through phishing-resistant authentication. Most IVIP platforms identify authentication gaps and stop there, leaving remediation to other tools or manual processes. Because Axiad Mesh integrates with Axiad Conductor, it can close the authentication gaps it finds -- deploying phishing-resistant credentials, enforcing MFA, and retiring legacy authentication methods -- within the same platform workflow.
The second is PKI and certificate intelligence. Axiad's background in PKI and credential lifecycle management means Mesh has deeper visibility into certificates, cryptographic assets, and credential sprawl than platforms that came to identity from a governance or cloud entitlements background. Mesh can discover certificate sprawl, track expiration dates, identify quantum-vulnerable cryptographic algorithms (RSA, ECC), and build a crypto-agility roadmap for post-quantum cryptography readiness -- capabilities that are largely absent from competing IVIP tools.
The third is financial risk quantification. While most IVIP platforms produce risk scores, Axiad Mesh's FAIR-based ALE reporting translates identity risk into probable dollar-denominated loss exposure. This matters for organizations where identity security investment decisions happen at the board or CFO level, not just the security team.
Key Use Cases for Axiad Mesh
Zero Trust implementation. Axiad Mesh maps every identity's effective permissions across the enterprise and continuously monitors for drift, giving Zero Trust programs the real-time visibility they need to enforce least-privilege access in practice rather than policy.
Identity attack surface reduction. Mesh identifies and helps eliminate over-privileged accounts, dormant credentials, toxic permission combinations, and shadow identities that expand the organization's exposure to credential-based attacks.
Non-human identity governance. Mesh discovers every service account, API key, certificate, and cloud role in the environment, tracks ownership and usage, monitors for unusual behavior, and surfaces machine identities with excessive or inappropriate access.
Compliance and audit readiness. Mesh generates audit-ready reports showing who has access to what, when access was granted, and by whom -- supporting SOC 2, ISO 27001, PCI DSS, CMMC, and NIST 800-171 requirements without requiring days of manual data collection across siloed systems.
AI agent security. As organizations deploy autonomous AI agents that call APIs, provision resources, and make decisions without direct human oversight, those agents operate as high-privilege identities that largely bypass traditional IAM controls. Mesh provides visibility into AI agent identities, monitors their access patterns, and applies the same governance rigor as human users.
Post-quantum cryptography readiness. Mesh discovers every certificate and cryptographic asset in the environment, identifies algorithms vulnerable to quantum computing threats, and helps organizations build a migration roadmap to post-quantum standards before the threat becomes operational.
Executive risk reporting. Mesh's FAIR-based financial quantification gives CISOs and security leaders board-ready data on identity risk exposure, demonstrating security improvements over time and connecting identity posture to business impact in terms executives and directors can act on.
Who Axiad Mesh Is Built For
Axiad Mesh is designed for large enterprises with complex, fragmented identity environments. The organizations that get the most value from it tend to share a few characteristics.
They have mature IAM investments but still lack a unified view. If your IGA, PAM, ITDR, and identity providers are operating in silos, Mesh is the connective layer that brings their data together. It doesn't replace those investments -- it makes them more effective by providing the cross-system context they individually can't produce.
They operate in regulated industries. Financial services, healthcare, insurance, and critical infrastructure organizations facing regulatory pressure to demonstrate measurable identity security posture -- not just point-in-time audit readiness -- are a strong fit. So are Defense Industrial Base contractors under CMMC and NIST 800-171 requirements, where demonstrable identity controls across complex, heterogeneous environments are increasingly mandatory.
They need to communicate identity risk in financial terms. Security teams that have to justify identity investment to a CFO or board need more than a list of open findings. Mesh's ALE-based risk reporting gives those teams the data to connect identity posture to business exposure in a language that drives decisions.
They are managing non-human identities at scale. Organizations where machine identities significantly outnumber human users -- common in mature cloud environments -- need visibility that traditional IAM tools weren't built to provide. Mesh treats human and non-human identities with equal rigor.
Frequently Asked Questions
What is Axiad Mesh?
Axiad Mesh is an Identity Visibility and Intelligence Platform (IVIP) that identifies, quantifies, and helps remediate identity risk across an organization's entire environment -- human and non-human, on-premises and cloud, across all IAM tools and identity providers. It integrates with existing identity infrastructure to correlate fragmented identity data into a unified risk picture and translates that risk into financial exposure using FAIR-based ALE reporting.
Is Axiad Mesh an ISPM tool?
No. Axiad Mesh is an IVIP, which is a broader category than ISPM. Identity Security Posture Management (ISPM) focuses on identity hygiene -- finding over-privileged accounts, misconfigurations, and access governance gaps within specific systems. Axiad Mesh aggregates data from ISPM tools alongside data from across the entire identity stack and produces a unified, scored, financially quantified view of risk across the full environment. ISPM findings are one input to what Mesh does; Mesh is the layer that makes those findings actionable in context.
How does Axiad Mesh differ from Veza?
Both Axiad Mesh and Veza are IVIP platforms that provide cross-system identity visibility and risk intelligence. Axiad Mesh's primary differentiators are its native integration with Axiad Conductor for phishing-resistant authentication remediation, its PKI and certificate intelligence capabilities, and its FAIR-based financial risk quantification. Veza's primary differentiator is its Access Graph, which maps effective permissions across hybrid environments with depth in SaaS and cloud entitlements.
What is the relationship between Axiad Mesh and Axiad Conductor?
Axiad Conductor is Axiad's FedRAMP-authorized phishing-resistant authentication platform that automates the full credential lifecycle. Mesh and Conductor integrate directly: when Mesh identifies authentication gaps -- weak MFA coverage, undeployed phishing-resistant credentials, legacy authentication still in use -- Conductor provides the remediation capability to close them. This makes Axiad's platform distinctive among IVIP vendors, most of which identify authentication gaps but rely on separate tools or manual processes to remediate them.
Does Axiad Mesh replace existing IAM tools?
No. Axiad Mesh integrates with your existing IAM stack rather than replacing it. It connects data from IGA, PAM, ITDR, ISPM, identity providers, directories, SaaS platforms, and secrets management to produce unified risk intelligence. Organizations that already have ISPM, ITDR, or other identity tools will get more value from those investments by adding Mesh as the unifying intelligence layer.
How does Axiad Mesh handle machine identities?
Axiad Mesh provides full visibility into non-human identities -- service accounts, API keys, OAuth tokens, certificates, cloud roles, and AI agents -- alongside human identities. It tracks their lifecycle, usage, and blast radius across the enterprise environment, surfaces excessive or inappropriate access, and applies the same risk scoring and governance rigor as human user identities.
Axiad Mesh is an Identity Visibility and Intelligence Platform (IVIP) that gives enterprises a unified view of identity risk across every human and non-human identity in their environment. Learn more at axiad.com/axiad-mesh.
Get Your Complimentary FAIR® Identity Risk Analysis
LIMITED TIME OFFER
See your identity risk quantified in financial terms. Axiad Mesh will analyze your environment and deliver a comprehensive FAIR assessment showing probable loss exposure, risk prioritization, and investment recommendations—at no cost.

Your Free Report Includes:
- Financial Risk Quantification - Probable annual loss exposure in dollar amounts
- Risk Prioritization - Top identity risks ranked by financial impact
- ROI Projections - Expected returns on identity security investments
Request Your Free FAIR® Analysis Today
No software purchase required, and completely confidential!*
*Trusted by federal agencies and Fortune 500 enterprises to secure their identity fabric


























%201.avif)